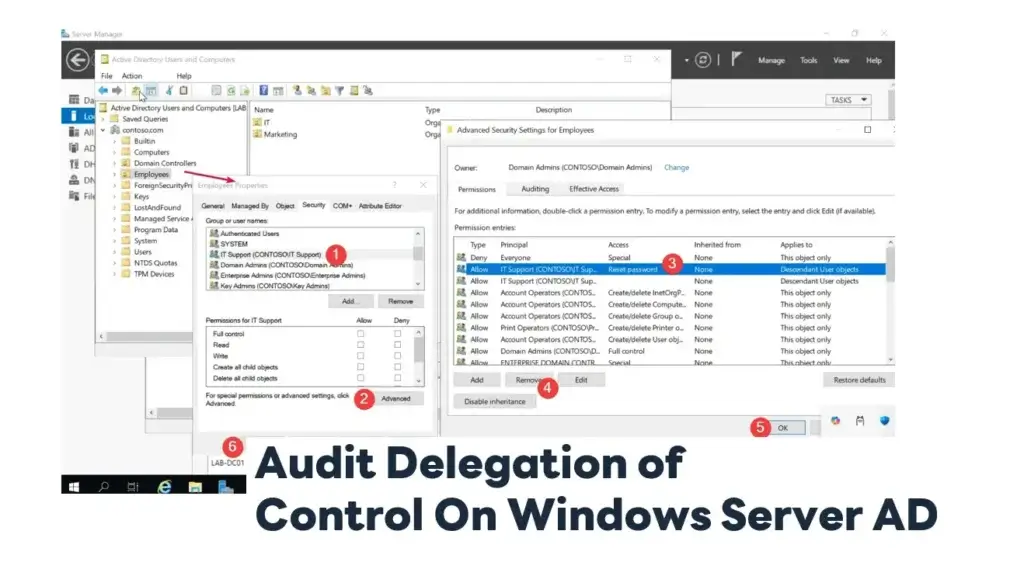
If you wants the Audit Delegation of Control that previously granted Delegation of Control rights such as Reset Password or Join Domain, you can refer to the following steps:
Using Active Directory Users and Computers (GUI)
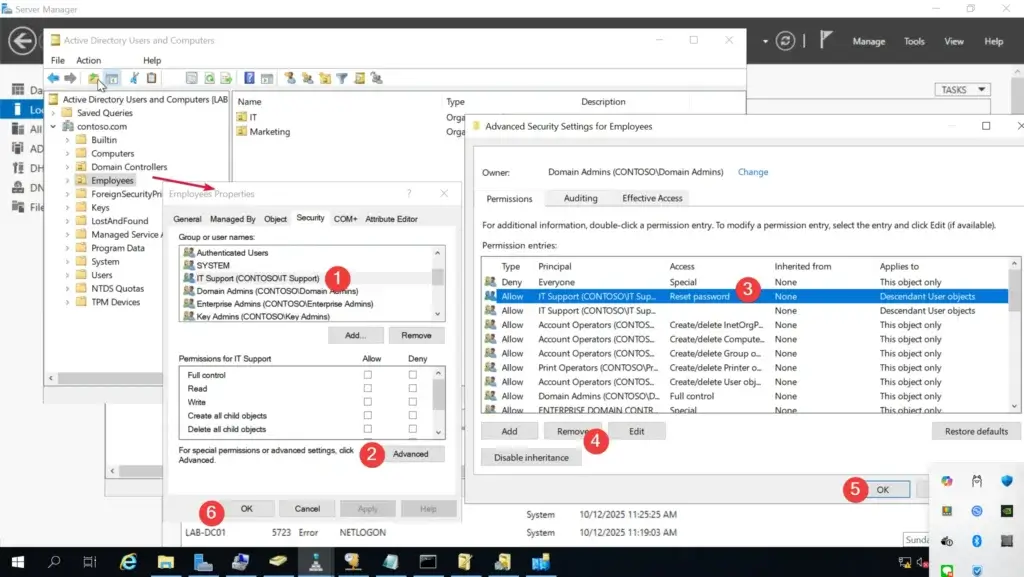
Open Active Directory Users and Computers (ADUC).
- Right-click an OU > Properties > Security tab.
- Click Advanced to see all permissions and their inheritance.
- Review entries that are not “inherited” and target accounts/groups that are not standard built-in groups (e.g., Domain Admins, Enterprise Admins).
These custom permissions are typically the result of Delegation of Control wizard assignments. if you want to remove
- Select Permission and Click Remove / if you want to add or edit let do its
- OK
- OK Again
Using PowerShell Script
you can use some cmdlet like Get-ADOrganizationalUnit / Get-Acl or Get-ADPermission etc. to grap data and visualize
Import-Module ActiveDirectory
Get-ADOrganizationalUnit -Filter * | ForEach-Object {
$ou = $_
$acl = Get-Acl -Path ("AD:\" + $ou.DistinguishedName)
$acl.Access | Where-Object { -not $_.IsInherited } | ForEach-Object {
[PSCustomObject]@{
OU = $ou.Name
IdentityReference = $_.IdentityReference
ActiveDirectoryRight= $_.ActiveDirectoryRights
AccessControlType = $_.AccessControlType
ObjectType = $_.ObjectType
}
}
} | Format-Table -AutoSize
Using dsacls.exe
You can use the dsacls.exe command-line tool to view permissions on individual OUs:
dsacls "OU=Sales,DC=contoso,DC=com"
Use AD ACL Scanner
- Enumerate permissions on OUs, users, groups, computers, and other AD objects.
- Filter and search for explicit (non-inherited) permissions, which are typically set via Delegation of Control.
- Export reports (CSV, Excel.) for compliance or review.
- Identify users/groups with non-standard or potentially risky permissions.
- Help satisfy audit requirements for reviewing delegated permissions.
Reference: https://github.com/canix1/ADACLScanner
Discover more from naiwaen@DebuggingSoft
Subscribe to get the latest posts sent to your email.